Elevate Your Security Posture with Snowflake Trust Center Detections

In today’s dynamic threat landscape, enterprise security teams need more than just compliance controls and best practices; they need proactive, near real-time intelligence to combat sophisticated attacks.
At Snowflake, we are committed to helping customers continuously secure their data and accounts with built-in security capabilities. In support of that, we have launched Trust Center detection findings to equip Snowflake customers with important security signals to help them stay up to date with potentially anomalous or suspicious activity in their accounts.
Beyond configurations: Understanding the shift to detections
Until now, the Snowflake Trust Center focused on surfacing violations findings with prescriptive, configuration-based remediation that is delivered only after a scheduled scanner runs.
Detection findings represent a significant evolution in Trust Center monitoring capabilities with a focus on potentially suspicious activity.
Capability |
Violations |
Detections |
Example(s) |
Non-MFA-enabled human users; missing network policy |
Logins from known malicious IP addresses; sensitive parameter changes |
Finding Type |
Configuration/policy noncompliance |
Discrete anomalous or potentially suspicious activity |
Remediation |
Prescriptive; requires a configuration change |
Nonprescriptive; signals for customer scrutiny and action |
Surfacing |
Only after a scanner runs |
Can be surfaced asynchronously (near real time for event-based) |
Management |
Notifications can be suppressed via Findings lifecycle management |
Signals an urgent need for review, so no explicit controls to suppress notifications |
Aggregated Visibility |
Yes, via the organization account; requires new GLOBALORGADMIN role |
Future |
The core security benefits of detections
Proactive threat intelligence at your fingertips
The goal of detections findings is to detect and surface unique, anomalous or activity signals that traditional methods might miss. These include:
Suspicious logins
Dormant user logins
Privilege escalation
Abnormal account activities (such as long-running queries or high query error rates)
Change in security policies (for example, authentication, network, session or password)
Suspicious data movement (coming soon)
End-of-life (EOL) warnings for drivers (coming soon)
Consolidated visibility and reduced blind spots
Without a native security signal, customers often rely on third-party solutions or spend significant effort building their own bespoke monitoring. Detections address this by:
Consolidating findings: Within a single account, customers can now see both violations and detections findings in one location.
Reducing manual effort: Customers can leverage the detections findings to gain insights into their security posture, reducing the manual effort of gathering this information from ad hoc queries.
Seamless integration into your security ecosystem
We recognize that enterprise customers often aggregate security data in their security operations center (SOC). That’s why Webhook integration (private preview) is a priority for what's coming next. Webhooks will allow for a near real-time, low-latency aggregation of Trust Center findings, enabling you to send detections directly to your existing SOC tools for immediate, centralized response.
Accelerated investigation and response
The Detections tab is designed for quick action:
Entity details: Our findings provide critical entity details, such as which users are exhibiting anomalous behavior.
Deep dive: Clicking a detection brings up a side panel with additional information and an “Open in Worksheet” button, allowing analysts to dive even deeper into the raw data. This is a correlation engine built for surfacing related findings.
Balancing risk reductions with tunable controls
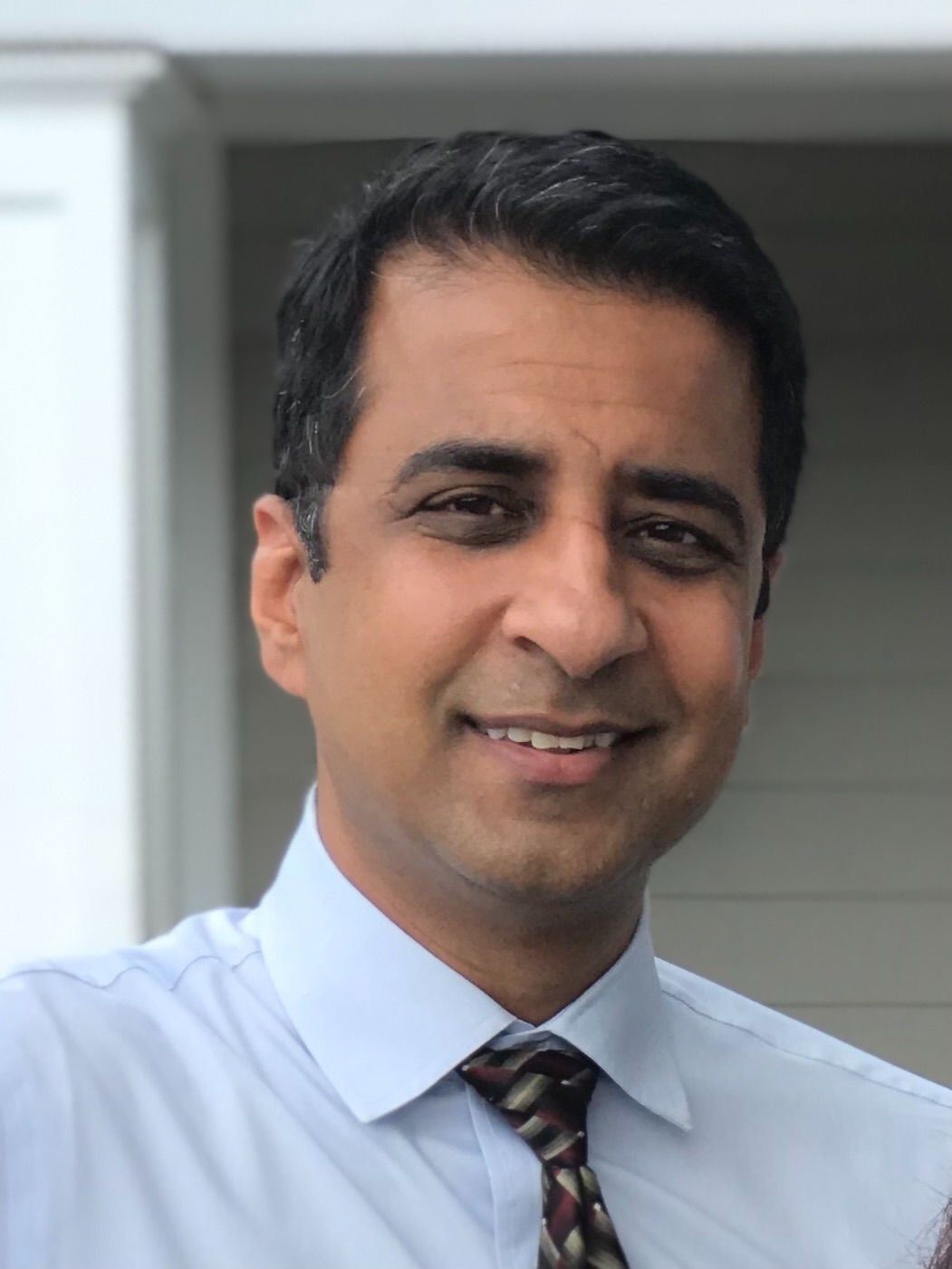
The new scanners are automatically enabled for most Snowflake customers who had previously enabled the Threat Intelligence Package and would benefit from the new capabilities. We made this decision in order to help protect our customers and reduce security risks, keeping continuous security improvements as our north star under our shared destiny model. Customers continue to maintain full control.
This new capability comes at additional costs and we recommend using it to enhance your security monitoring. However, you have the option to disable the new event-driven scanners and/or modify their schedule within the “Manage Scanners” tab. In aggregate, the new scanners incur fewer than two credits per day, similar to the cost of a cup of coffee (see Figure 1).
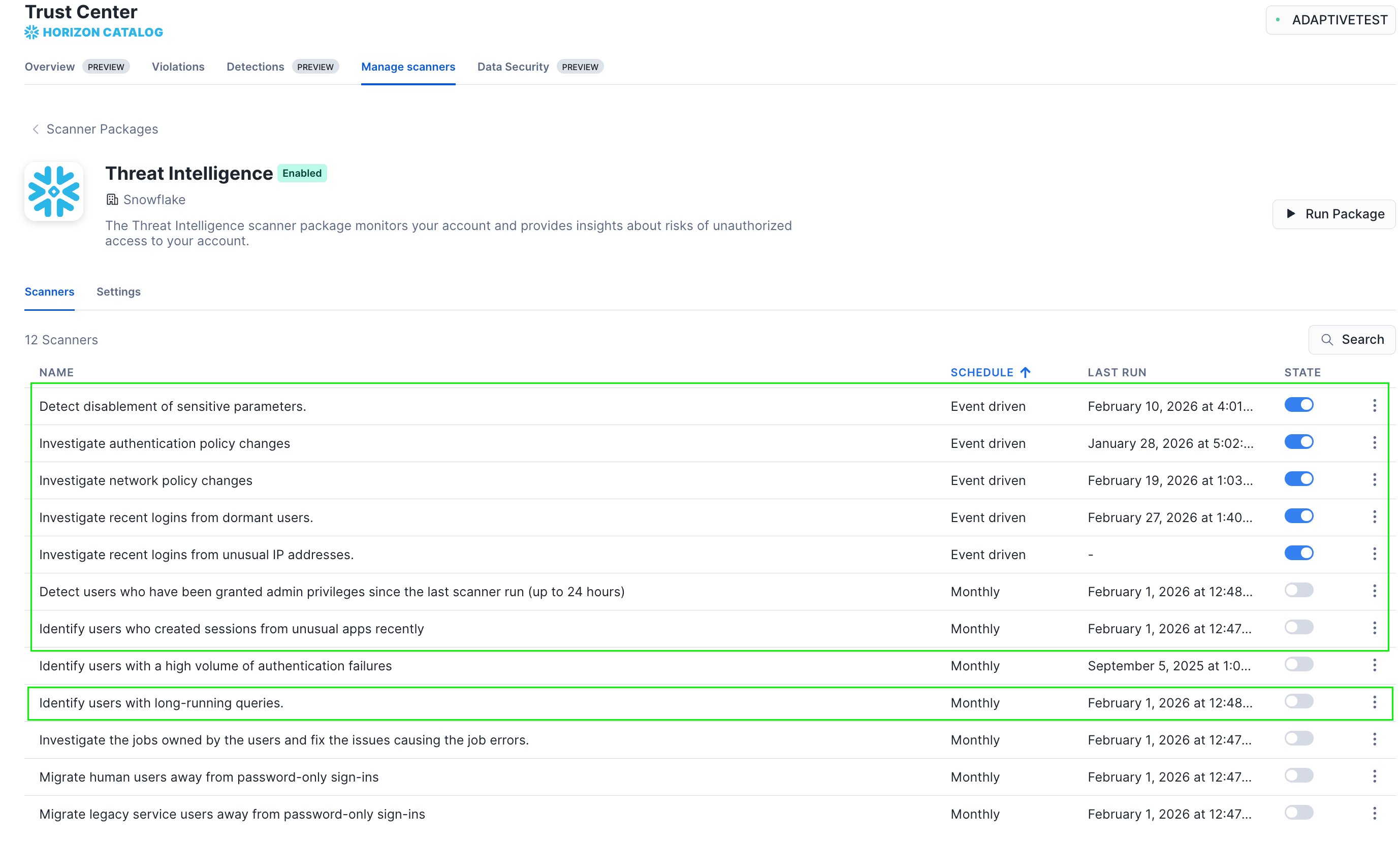
Get started today
We encourage you to use detections to continuously monitor and enhance the security controls governing your Snowflake accounts. Start by visiting the Trust Center in Snowsight. You will notice that the Findings tab has been renamed Violations, and a new Detections tab has been added to the UI (see Figure 2). Further details are available in Snowflake documentation.
Security is a shared responsibility, and Trust Center detection findings are our latest tool to empower your team to tackle the complex security challenges of the cloud and AI era.